The Definitive 6-Step Plan for Strengthening IoT Security

The Internet of Things (IoT) has become a transformative force in our lives. From homes and offices to vehicles and personal wearables, digitally connected devices are now pervasive. In fact, as the IoT landscape expands exponentially, the number of IoT connections worldwide will surpass 83 billion by 2024, facilitating massive data exchange. However, with this surge in IoT adoption, the cyber threat surface has also increased. Today, safeguarding IoT connections is a prime priority.
So, in this blog, we'll walk you through the following steps for strengthening IoT security:
Evaluate IoT Device Characteristics

To enhance IoT security, start by evaluating the characteristics of your IoT devices. Understand their capabilities and potential vulnerabilities. This assessment lays the foundation for a comprehensive security plan tailored to your specific devices.
Even before integrating IoT devices into your network, thoroughly assess their security features and vulnerabilities.
- Consider factors like firmware updates, built-in security controls, device management capabilities, etc.
- Also, consider regular capabilities like connectivity, intelligence, heterogeneity, etc., to be sure you’ll have the information you need to implement effective security controls.
In sum, choose devices that support strong security standards and regular updates to minimize potential risks. This dissecting of the intricate attributes of IoT devices allows for laying a solid groundwork for a comprehensive IoT security plan that meets your needs while minimizing security risks.
Do more with Test Automation
Discover more ways to add ‘low-code no-code‘ test automation in your workflows
Educate the Team About IoT Security
Educating your employees on IoT security is vital to preventing unwitting security risks. This way, they are best placed to recognize potential security threats and respond quickly. That said, here's what you can do:
Explain the Risks of IoT Devices
IoT devices can become vulnerable to security risks as they support features like powerful analytics, real-time processing, and a host of other functionalities. Also, they can operate independently in certain scenarios without regular maintenance or oversight.
Educating the team helps employees understand how to minimize these risks. For instance, employees will better understand why they should avoid connecting IoT devices to insecure networks or opening them to hostile ports.
Teach How to Identify Phishing Attacks
Phishing attacks are immensely pervasive, so much so that they constitute 36% of all data breaches in the US. These attacks are a viable means for malicious actors to solicit sensitive information or install malware on the target device.
Given that we are more connected than ever with smart homes and autonomous vehicles, this stolen information can wreak havoc. Besides, a study, while stressing the severity of phishing attacks, outlines that about 98% of the traffic via IoT devices is unencrypted. So, educating the team on alleviating such threats is critical.
- For that reason:Conduct social engineering pen tests to identify vulnerable individuals.
- Train employees to recognize phishing attempts and practice secure behaviors, especially with remote work setups and personal devices connected to the organizational network.
Create an Incident Response Plan
As elucidated above, you should commence by evaluating the characteristics of your IoT devices. Once you're well aware of their capabilities and potential vulnerabilities, it becomes easier to create a framework for a relatively comprehensive security plan tailored to your specific devices.
Develop an effective incident response plan to address security breaches swiftly. Ideally, this plan should encompass the fundamental understanding of the threat landscape, i.e., the risks that the IoT devices are exposed to. It must also define the:
- What(s) and how(s) of alerting the relevant stakeholders
- Backup and recovery mechanisms
- Process for the post-incident analysis
Assign tasks and responsibilities to handle security incidents promptly and efficiently. Also, regularly test the plan to ensure its effectiveness and alignment with the changing threat landscape.
Download the 100% Free Guide
Master the essentials of advanced approach
to object recognition.

Establish a Framework for Access Management
IoT devices often connect to critical data and systems. So, it is essential to limit access to these devices and systems by implementing the principle of least privilege. This means that only authorized users have specific access to the necessary activities.
You can use Identity Governance and Administration (IGA) solutions to help you manage permissions effectively. IGA solutions can help:
- Track who has access to what
- Revoke access when it is no longer needed.
In addition to IGA solutions, you should also implement a layered approach to access control. This means you should use multiple layers of security to protect your devices and systems. For example, you could use a combination of passwords, two-factor authentication, and physical access controls to protect the network.
Keep Encryption as Default
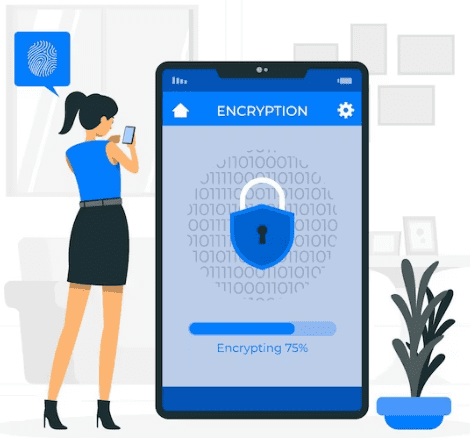
We mentioned above that 98% of the IoT traffic is unencrypted. But why is that the case? Well, enterprise IoT networks often constitute thousands of devices spread across the enterprise ecosystem. They have a lot of endpoints and constantly moving data (between the hub, gateway, and the cloud). All such moving data needs to be encrypted if encryption has to work, which can prove to be an immensely challenging endeavor.
However, regardless of the complexity, encryption is critical for curbing any unauthorized access. Therefore, enterprises must ensure that they are encrypting connections by default, i.e., encryption is the default setting for your IoT devices and communication channels.
Besides encryption, emphasis must also be laid on evaluating the latest firmware version. Enterprises need to check for security patches and updates and install them promptly to keep their devices secure. For critical systems that handle sensitive data, configure manual updates to ensure that no unauthorized personnel can install malware into them. Also, be careful about plugging in devices at public places like airports or cafes, even if you are using a public Wi-Fi connection.
Automate IoT Security
As the scale of IoT deployments grows, manual security management becomes impractical. So, regularly scan your system using vulnerability assessment tools to identify potential weaknesses proactively. Implement Network Traffic Analysis (NTA) solutions to detect anomalous activities and swiftly respond to compromised devices.
In fact, here are some security tasks that you can automate:
- Vulnerability scanning: Vulnerability scanning can unearth known vulnerabilities in your IoT devices and drive the pertinent security efforts to patch them.
- Intrusion detection: Intrusion detection is vital for detecting and responding to attacks. It does so by monitoring IoT devices for any malicious activity.
- Patch management: Patch management serves to keep IoT devices up to date with the latest security patches to keep them at bay from known vulnerabilities.
- Device management: Device management can track and manage your IoT devices to ensure they are configured securely and not used maliciously.
In a Nutshell
With billions of devices now connected to the Internet, IoT has well and truly become a way of life. But this tremendous connectivity has also made IoT devices a target for cyberattacks. It's here that the need for a concrete IoT security plan becomes apparent. From developing a profound understanding of the device's characteristics to training the teams on handling an IoT security breach, a comprehensive IoT security plan can be an invaluable asset to your organization.
Geosley Andrades
Director, Product Evangelist at ACCELQ
Geosley is a Test Automation Evangelist and Community builder at ACCELQ. Being passionate about continuous learning, Geosley helps ACCELQ with innovative solutions to transform test automation to be simpler, more reliable, and sustainable for the real world.
Discover More
 Oracle Cloud ERP Implementation with Automation Testing Strategy
Oracle Cloud ERP Implementation with Automation Testing Strategy
Oracle Cloud ERP Implementation with Automation Testing Strategy
 Don’t Do It the Wrong Way – Tips for Testing in Production
Don’t Do It the Wrong Way – Tips for Testing in Production